an email newsletter released every month highlighting the latest articles, events, technical inquiries, and voices from the community
Cybersecurity & Information Systems Digest
The Digest is a newsletter intended to provide readers with a greater awareness of the latest research and development trends in the four technical focus areas supported by CSIAC while also highlighting recent CSIAC activities, services, and products.
Current Digest
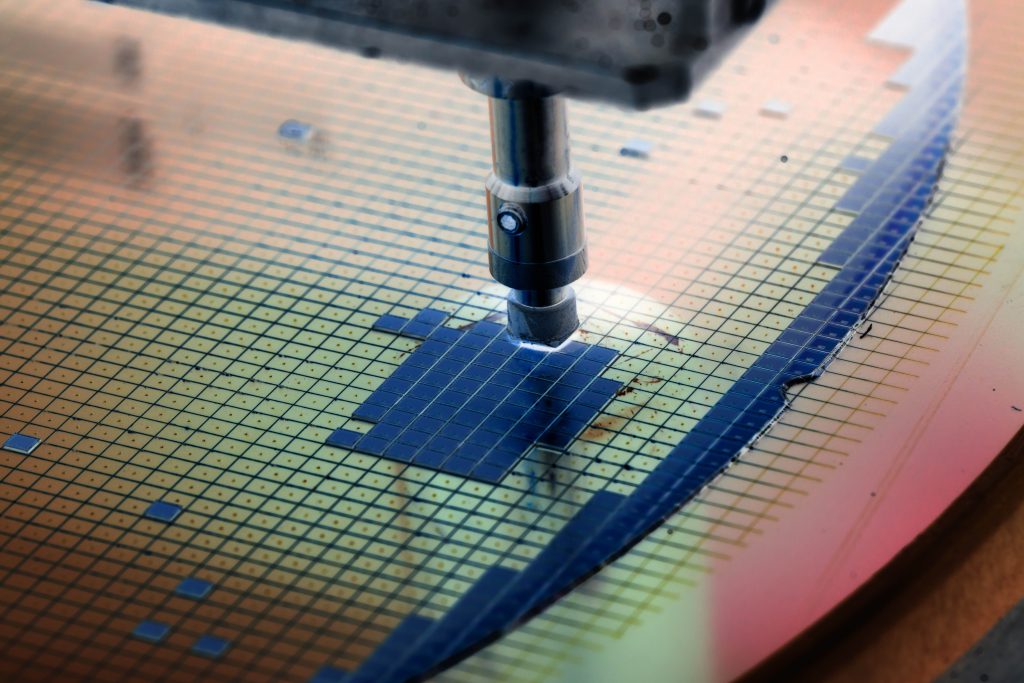
Microelectronics Overview
Cybersecurity and Information Systems Analysis Center subject matter experts, experienced with delivering presentations to senior leadership on technical topics, conducted open-source research for relevant information on microelectronics and its impact on the U.S. Department of…
DoD CIO Establishes Cybersecurity Training Provider Marketplace
The Defense Acquisition University (DAU) is now represented in the new DoD 8140 Cyber Workforce (DCWF) Qualification Provider Marketplace online. Intended for DCWF personnel, the Marketplace is a time-saving platform that utilizes a simplified search…
Stay up to date with our Digest
Receive the latest issue straight to your inbox