an email newsletter released every month highlighting the latest articles, events, technical inquiries, and voices from the community
Cybersecurity & Information Systems Digest
The Digest is a newsletter intended to provide readers with a greater awareness of the latest research and development trends in the four technical focus areas supported by CSIAC while also highlighting recent CSIAC activities, services, and products.
Current Digest
Artificial Intelligence (AI)/Machine-Learning (ML) Transition Timetable
Cybersecurity and Information Systems Information Analysis Center (CSIAC) subject matter experts from BluePath Labs (BPL) attempted to answer how fast the PRC can transition AI/ML technologies from the lab to the field. Although information was…
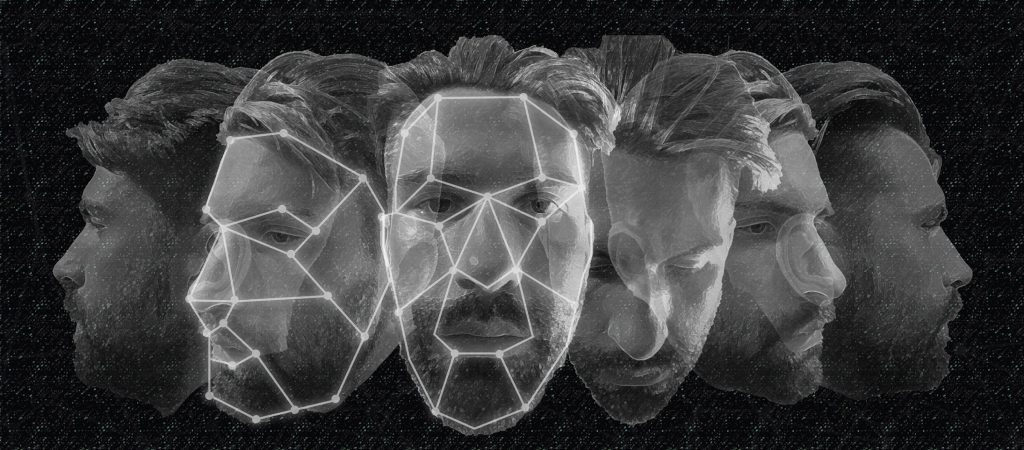
Deepfake Defense Tech Ready for Commercialization, Transition
The threat of manipulated media has steadily increased as automated manipulation technologies become more accessible and social media continues to provide a ripe environment for viral content sharing. The speed, scale, and breadth at which…
Stay up to date with our Digest
Receive the latest issue straight to your inbox