Carriers no longer want their speciality pizzas delivered in a box, fully baked with pre-determined toppings. In fact they figure that it is economical to purchase standard pizza ingredients wholesale, bake ginormous crusts and believe they can please their customers faster by delivering custom toppings by slice on demand.
Network function virtualisation (NFV) effectively takes carriers out of the “pizza” box by dismantling the content of numerous proprietary devices and classic network appliances into their rudimentary components: software, compute, storage and network. This effectively blows open the carriers box based security architectures, perimeters and controls. Carriers need to monitor the integrity of resources as physical server firmware, hypervisors, guest operating systems to ensure customers’ sensitive data is secure on their cloud. This brings carriers to rethink forgotten threat vectors on the redefined, yet age-old attack surface that will dominate and pervade the high volume commodity infrastructure: Firmware.
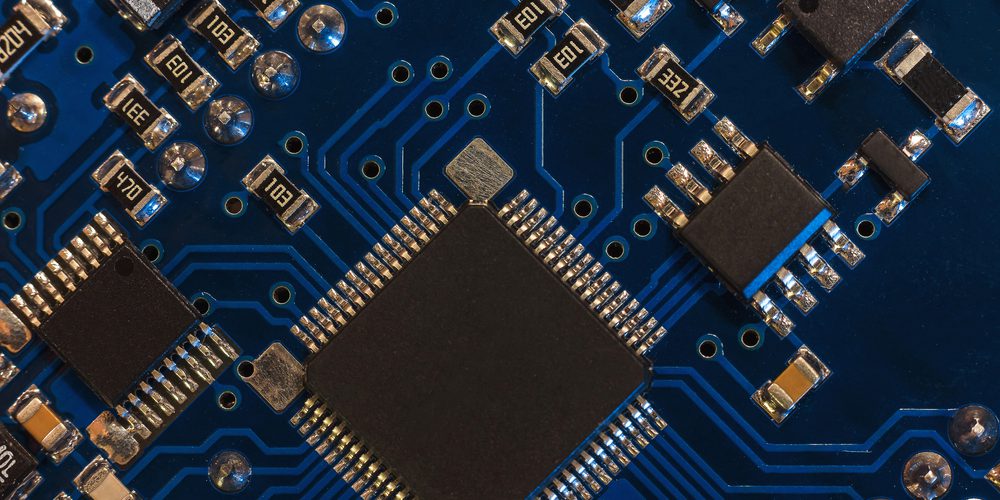
Firmware is the first code run by a system and is typically written on read only memory (ROM) chips soldered onto circuit boards ranging from BIOS chips on the motherboard to controller chips of peripheral devices. Unified extensible firmware interface (UEFI) is a more generic type of computer firmware standard, invoked during the boot process in newer systems. Firmware can be found on USB drives, hard drives, keyboards, SD cards, RAID controllers, SSDs, network cards, video and audio cards among others. Almost every electronic device today has rewritable firmware chips. Embedded software/firmware in field programmable gate arrays (FPGA), application specific integrated circuits (ASIC), application specific standard products (ASSP), system on a chip (SOC) and firmware embedded systems are widely found throughout every industry.
![Figure 1: [1] [2]](https://csiac.org/wp-content/uploads/2016/07/Bhasker-Fig1-1024x630.jpg)
Figure 1: [1] [2]